[20191127]表 full Hash Value的计算.txt --//曾经做过表full Hash Value的计算,当时我是通过建立简单的schema以及表名的形式,使用hashcat破解oracle的 --//表 full Hash Value的计算,参考链接: http://blog.itpub.net/267265/viewspace-2149366/ => [20171227]表的FULL_HASH_VALUE值的计算 http://blog.itpub.net/267265/viewspace-2214232/ => [20180914]oracle 12c 表 full_hash_value如何计算.txt --//得到的结论是: --//表的FULL_HASH_VALUE计算就是table_name.owner加上"\01\0\0\0". --//12c引入了PDB,表的full_hash_value是table_name.owner.con_name\01\0\0\0的md5sum值. --//昨天看了一篇博客,链接https://mvelikikh.blogspot.com/2019/07/vdbpipes-unveiling-truth-of-oracle-hash.html --//作者通过DebugTrace获得oracle内部函数,主要通过kggmd5Update,确定里面参与运算的字符. --//我仅仅重复作者的测试验证这个过程: 1.环境: SYS@book> @ ver1 PORT_STRING VERSION BANNER ------------------------------ -------------- -------------------------------------------------------------------------------- x86_64/Linux 2.4.xx 11.2.0.4.0 Oracle Database 11g Enterprise Edition Release 11.2.0.4.0 - 64bit Production 2. 定位相关内部函数: $ gdb $(which oracle ) GNU gdb (GDB) Red Hat Enterprise Linux (7.0.1-45.el5) Copyright (C) 2009 Free Software Foundation, Inc. License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html> This is free software: you are free to change and redistribute it. There is NO WARRANTY, to the extent permitted by law. Type "show copying" and "show warranty" for details. This GDB was configured as "x86_64-redhat-linux-gnu". For bug reporting instructions, please see: <http://www.gnu.org/software/gdb/bugs/>... Reading symbols from /u01/app/oracle/product/11.2.0.4/dbhome_1/bin/oracle...(no debugging symbols found)...done. (gdb) disassemble kglComputeHash ... 0x00000000098445d8 <kglComputeHash+96>: movl $0xefcdab89,0x4(%r9) 0x00000000098445e0 <kglComputeHash+104>: mov -0x48(%rbp),%r10 0x00000000098445e4 <kglComputeHash+108>: movl $0x98badcfe,0x8(%r10) 0x00000000098445ec <kglComputeHash+116>: mov -0x48(%rbp),%r11 0x00000000098445f0 <kglComputeHash+120>: movl $0x10325476,0xc(%r11) 0x00000000098445f8 <kglComputeHash+128>: mov 0x10(%r15),%rsi 0x00000000098445fc <kglComputeHash+132>: mov (%r15),%edx 0x00000000098445ff <kglComputeHash+135>: callq 0x97f09a4 <kggmd5Update> 0x0000000009844604 <kglComputeHash+140>: movzbl 0x8(%r15),%eax 0x0000000009844609 <kglComputeHash+145>: test %eax,%eax 0x000000000984460b <kglComputeHash+147>: je 0x984463a <kglComputeHash+194> 0x000000000984460d <kglComputeHash+149>: lea -0x90(%rbp),%rdi 0x0000000009844614 <kglComputeHash+156>: lea 0x6359d1(%rip),%rsi # 0x9e79fec <_2__STRING.98.0> 0x000000000984461b <kglComputeHash+163>: mov $0x1,%edx 0x0000000009844620 <kglComputeHash+168>: callq 0x97f09a4 <kggmd5Update> ... --//你可以发现多处kggmd5Update的调用. 3.建立gdb脚本: $ cat md5.gdb set pagination off break kggmd5Update commands printf "Length: %d\n",$rdx x/8xc $rsi c end break kglComputeHash commands c end break kggmd5Process commands c end break kggmd5Finish commands c end --//session 1: SCOTT@book> @ spid SID SERIAL# PROCESS SERVER SPID PID P_SERIAL# C50 ---------- ---------- ------------------------ --------- ------ ------- ---------- -------------------------------------------------- 75 751 21617 DEDICATED 21618 29 156 alter system kill session '75,751' immediate; --//session 2: $ gdb -p 21618 -x md5.gdb ... Breakpoint 1 at 0x97f09a8 Breakpoint 2 at 0x984457c Breakpoint 3 at 0x97f14be Breakpoint 4 at 0x97f0830 --//session 1: SCOTT@book> desc emp Name Null? Type -------- -------- ------------ EMPNO NOT NULL NUMBER(4) ENAME VARCHAR2(10) JOB VARCHAR2(9) MGR NUMBER(4) HIREDATE DATE SAL NUMBER(7,2) COMM NUMBER(7,2) DEPTNO NUMBER(2) --//session 2,按c继续: Breakpoint 2, 0x000000000984457c in kglComputeHash () Breakpoint 1, 0x00000000097f09a8 in kggmd5Update () Length: 3 0x7faa77e1fca8: 69 'E' 77 'M' 80 'P' 0 '\000' 0 '\000' 0 '\000' 0 '\000' 0 '\000' --//length=3,EMP对应表 Breakpoint 1, 0x00000000097f09a8 in kggmd5Update () Length: 1 0x9e79fec <_2__STRING.98.0>: 46 '.' 0 '\000' 0 '\000' 0 '\000' 107 'k' 116 't' 99 'c' 110 'n' --//length=1 ,小数点. Breakpoint 1, 0x00000000097f09a8 in kggmd5Update () Length: 5 0x863db2f4: 83 'S' 67 'C' 79 'O' 84 'T' 84 'T' 0 '\000' 0 '\000' 0 '\000' --//length=5 ,SCOTT就是owner. Breakpoint 1, 0x00000000097f09a8 in kggmd5Update () Length: 4 0x7fffbb155800: 1 '\001' 0 '\000' 0 '\000' 0 '\000' -1 '' 127 '\177' 0 '\000' 0 '\000' --//length=4 ,字符'\001\000\000\000' Breakpoint 4, 0x00000000097f0830 in kggmd5Finish () Breakpoint 1, 0x00000000097f09a8 in kggmd5Update () Length: 43 0xbefbe20 <kggmd5padding.0>: -128 '\200' 0 '\000' 0 '\000' 0 '\000' 0 '\000' 0 '\000' 0 '\000' 0 '\000' Breakpoint 1, 0x00000000097f09a8 in kggmd5Update () Length: 8 0x7fffbb155750: 104 'h' 0 '\000' 0 '\000' 0 '\000' 0 '\000' 0 '\000' 0 '\000' 0 '\000' --//这些字符拼接起来就是EMP.SCOTT\001\000\000\000,也就是表md5按照此内容计算. SYS@book> select dbms_crypto.hash(rawtohex('EMP.SCOTT'||chr(1)||chr(0)||chr(0)||chr(0)), 2) c40 from dual; C40 ---------------------------------------- 1EA14E682B60AB3ED11D8E77D1E781E2 --//1EA14E682B60AB3ED11D8E77D1E781E 按照4位反转就是 684ea11e 3eab602b 778e1dd1 0081e7d1 --//验证看看: SYS@book> select owner,name,namespace,type,hash_value,full_hash_value from V$DB_OBJECT_CACHE where owner='SCOTT' and name='EMP'; OWNER NAME NAMESPACE TYPE HASH_VALUE FULL_HASH_VALUE ------ ---- --------------- ----- ---------- -------------------------------- SCOTT EMP TABLE/PROCEDURE TABLE 3800164305 684ea11e3eab602b778e1dd1e281e7d1 --//对比反转后结果完全能对上.后面的chr(1)||chr(0)||chr(0)||chr(0)实际上与namespace有关.可以执行如下确定: --//select distinct kglhdnsp,kglhdnsd,kglobtyd from x$kglob order by 1; --//使用操作系统命令计算如下: $ echo -e -n 'EMP.SCOTT\01\0\0\0' | md5sum | sed 's/ -//' | xxd -r -p | od -t x4 | sed -n -e 's/^0000000 //' -e 's/ //gp' 684ea11e3eab602b778e1dd1e281e7d1 --//可以发现完成能对上.
[20191127]表 full Hash Value的计算.txt
来源:这里教程网
时间:2026-03-03 14:35:42
作者:
编辑推荐:
- [20191127]表 full Hash Value的计算.txt03-03
- Oracle数据库 11.2.0.4 EMON进程持续消耗CPU03-03
- 手机NFC有6种用法!很多人只会用公交卡,剩下5个功能也很强大03-03
- ORA-00904:"WM_CONCAT":标识符无效03-03
- SaCa Aclome 助力泉州数字云谷实现云管一体化03-03
- [20191122]oracel SQL parsing function qcplgte.txt03-03
- Streams AQ: enqueue blocked on low memory等待事件导致expdp导出缓慢问题03-03
- [20191122]schama建立同义词.txt03-03
下一篇:
相关推荐
-
雷神推出 MIX PRO II 迷你主机:基于 Ultra 200H,玻璃上盖 + ARGB 灯效
2 月 9 日消息,雷神 (THUNDEROBOT) 现已宣布推出基于英
-
制造商 Musnap 推出彩色墨水屏电纸书 Ocean C:支持手写笔、第三方安卓应用
2 月 10 日消息,制造商 Musnap 现已在海外推出一款 Oce
热文推荐
- Oracle数据库 11.2.0.4 EMON进程持续消耗CPU
Oracle数据库 11.2.0.4 EMON进程持续消耗CPU
26-03-03 - 手机NFC有6种用法!很多人只会用公交卡,剩下5个功能也很强大
手机NFC有6种用法!很多人只会用公交卡,剩下5个功能也很强大
26-03-03 - Streams AQ: enqueue blocked on low memory等待事件导致expdp导出缓慢问题
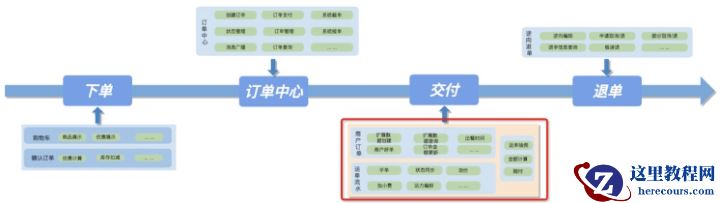
- 饿了么交付中心语言栈转型总结
饿了么交付中心语言栈转型总结
26-03-03 - [20191122]RMAN-03999.txt
[20191122]RMAN-03999.txt
26-03-03 - Oracle SQL执行计划异常解析的处理方法
Oracle SQL执行计划异常解析的处理方法
26-03-03 - Oracle分布式查询语句的性能优化
Oracle分布式查询语句的性能优化
26-03-03 - 生产库上在线不停机搭建dataguard
生产库上在线不停机搭建dataguard
26-03-03 - ORA-600:[qertbGetPartitionNumber:qesma2],[],[],[]
- 从电商到软件市场,阿里双11战火蔓延
从电商到软件市场,阿里双11战火蔓延
26-03-03






![[20191122]RMAN-03999.txt [20191122]RMAN-03999.txt](/d/file/efpub/2026/03-03/small8fb9eae65ae2d170b064b9daab9065701772519709.jpg)



![ORA-600:[qertbGetPartitionNumber:qesma2],[],[],[] ORA-600:[qertbGetPartitionNumber:qesma2],[],[],[]](https://www.herecours.com/d/file/efpub/2026/03-03/20260303135730836753.jpg?x-oss-process=style/bb)
