[20210128]拼接数据块.txt --//昨天测试[20210126]探究oracle内存分配4.txt,链接http://blog.itpub.net/267265/viewspace-2753605/ --//使用X$KSMMEM视图,实际上该视图可以看到共享内存段的全部信息,这样利用这个视图应该可以看到数据块的信息. --//测试使用它拼接数据块看看. 1.环境: SYS@book> @ ver1 PORT_STRING VERSION BANNER ------------------------------ -------------- -------------------------------------------------------------------------------- x86_64/Linux 2.4.xx 11.2.0.4.0 Oracle Database 11g Enterprise Edition Release 11.2.0.4.0 - 64bit Production 2.测试: SCOTT@book> select rowid,dept.* from dept; ROWID DEPTNO DNAME LOC ------------------ ---------- -------------- ------------- AAAVRCAAEAAAACHAAA 10 ACCOUNTING NEW YORK AAAVRCAAEAAAACHAAB 20 RESEARCH DALLAS AAAVRCAAEAAAACHAAC 30 SALES CHICAGO AAAVRCAAEAAAACHAAD 40 OPERATIONS BOSTON SCOTT@book> @ rowid AAAVRCAAEAAAACHAAB OBJECT FILE BLOCK ROW ROWID_DBA DBA TEXT ---------- ---------- ---------- ---------- -------------------- -------------------- ---------------------------------------- 87106 4 135 1 0x1000087 4,135 alter system dump datafile 4 block 135 ; SYS@book> set verify off SYS@book> @ bh 4 135 INST_ID HLADDR DBARFIL DBABLK CLASS CLASS_TYPE STATE TCH CR_SCN_BAS CR_SCN_WRP CR_UBA_FIL CR_UBA_BLK CR_UBA_SEQ BA LE_ADDR OBJECT_NAME ---------- ---------------- ---------- ---------- ---------- ------------------ ---------- ---------- ---------- ---------- ---------- ---------- ---------- ---------------- ---------------- -------------------- 1 0000000084D25320 4 135 1 data block xcur 1 0 0 0 0 0 0000000074B6E000 00 DEPT --//BA=0000000074B6E000. --//8192 = 0x2000 --//0x0000000074B6E000+0x2000 = 1958150144 = 0x74b70000 --//说明一点,如果KSMMMVAL全部是0,该视图显示: SYS@book> SELECT * FROM X$KSMMEM where addr=hextoraw('0000000074B6E1A0'); ADDR INDX INST_ID KSMMMVAL ---------------- ---------- ---------- ---------------- 0000000074B6E1A0 43441204 1 00 set head off set feedback off spool 4_135.txt SELECT KSMMMVAL FROM X$KSMMEM WHERE addr >= hextoraw('0000000074B6E000') and addr< hextoraw('0000000074B70000') and rownum<=1024; spool off --//感觉有点慢,加入rownum<=1024快一点点.仅仅等于可以使用内部索引. 3. 尝试观察: $ sed 's/^00$/00000000/' 4_135.txt | tail -1 8F1706014B524F59 BBED> dump /v offset 8184 File: /mnt/ramdisk/book/users01.dbf (4) Block: 135 Offsets: 8184 to 8191 Dba:0x01000087 ----------------------------------------------------------------------------------------------------------- 594f524b 0106178f l YORK.... --//1行8个字节,注意看由于CPU的大小头问题,完成是颠倒过来的.麻烦的是8个字节颠倒.od -t x8可以实现颠倒. $ sed 's/^00$/0000000000000000/' 4_135.txt | xxd -r -p | od -t x8 | cut -c9-| xxd -r -p | xxd -c 16 -g 2 | tail 0001f60: 6574 2f55 524c 436c 6173 734c 6f61 6465 et/URLClassLoade 0001f70: 7224 3402 c102 ff02 c11e 0778 7108 180c r$4.?.?.xq... 0001f80: 2e12 0778 7108 180c 2e12 0778 7108 180c ...xq......xq... 0001f90: 2e12 02c1 02ff ff02 c149 ff02 c107 04c3 ...?.罥.?.? 0001fa0: 2c00 0302 c129 0a4f 5045 5241 5449 4f4e ,...?.OPERATION 0001fb0: 5306 424f 5354 4f4e 2c00 0302 c11f 0553 S.BOSTON,...?.S 0001fc0: 414c 4553 0743 4849 4341 474f 2c00 0302 ALES.CHICAGO,... 0001fd0: c115 0852 4553 4541 5243 4806 4441 4c4c ?.RESEARCH.DALL 0001fe0: 4153 2c02 0302 c10b 0a41 4343 4f55 4e54 AS,...?.ACCOUNT 0001ff0: 494e 4708 4e45 5720 594f 524b 0106 178f ING.NEW YORK.... $ xxd -c16 -g 2 -s 1105920 -l 8192 /mnt/ramdisk/book/users01.dbf | tail 010ff60: 6574 2f55 524c 436c 6173 734c 6f61 6465 et/URLClassLoade 010ff70: 7224 3402 c102 ff02 c11e 0778 7108 180c r$4.?.?.xq... 010ff80: 2e12 0778 7108 180c 2e12 0778 7108 180c ...xq......xq... 010ff90: 2e12 02c1 02ff ff02 c149 ff02 c107 04c3 ...?.罥.?.? 010ffa0: 2c00 0302 c129 0a4f 5045 5241 5449 4f4e ,...?.OPERATION 010ffb0: 5306 424f 5354 4f4e 2c00 0302 c11f 0553 S.BOSTON,...?.S 010ffc0: 414c 4553 0743 4849 4341 474f 2c00 0302 ALES.CHICAGO,... 010ffd0: c115 0852 4553 4541 5243 4806 4441 4c4c ?.RESEARCH.DALL 010ffe0: 4153 2c02 0302 c10b 0a41 4343 4f55 4e54 AS,...?.ACCOUNT 010fff0: 494e 4708 4e45 5720 594f 524b 0106 178f ING.NEW YORK.... --//上下对比完全一致. $ diff <(sed 's/^00$/0000000000000000/' 4_135.txt | xxd -r -p | od -t x8 | cut -c9-| xxd -r -p | xxd -c 16 -g 2 | cut -c9-) <(xxd -c16 -g 2 -s 1105920 -l 8192 /mnt/ramdisk/book/users01.dbf| cut -c9- ) --//纯粹无聊,就算练习一些bash shell编程吧^_^.
[20210128]拼接数据块.txt
来源:这里教程网
时间:2026-03-03 16:23:15
作者:
编辑推荐:
下一篇:
相关推荐
-
雷神推出 MIX PRO II 迷你主机:基于 Ultra 200H,玻璃上盖 + ARGB 灯效
2 月 9 日消息,雷神 (THUNDEROBOT) 现已宣布推出基于英
-
制造商 Musnap 推出彩色墨水屏电纸书 Ocean C:支持手写笔、第三方安卓应用
2 月 10 日消息,制造商 Musnap 现已在海外推出一款 Oce
热文推荐
- unable to extend table SYS.AUD$ by 1024 in tablespace SYSTEM
- 【BUILD_ORACLE】使用ASMLib包搭建ASM磁盘
【BUILD_ORACLE】使用ASMLib包搭建ASM磁盘
26-03-03 - 干货 | 设计师必备中国风配色卡,快来收藏
干货 | 设计师必备中国风配色卡,快来收藏
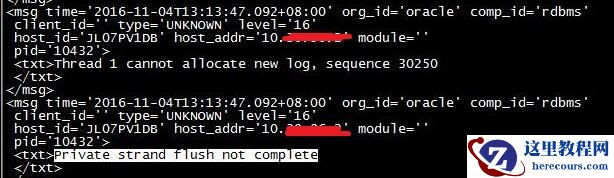
26-03-03 - Thread 1 cannot allocate new log
Thread 1 cannot allocate new log
26-03-03 - Oracle database 19c中获取当前数据库版本的方法
Oracle database 19c中获取当前数据库版本的方法
26-03-03 - Oracle如何删除表中重复记录保留第一条
Oracle如何删除表中重复记录保留第一条
26-03-03 - Oracle网络服务基础(二)之监听器与TNS配置管理
Oracle网络服务基础(二)之监听器与TNS配置管理
26-03-03 - ORACLE 数据库业务用户密码重置慎用特殊字符
ORACLE 数据库业务用户密码重置慎用特殊字符
26-03-03 - oracle优化之生产系统不改代码解决SQL性能问题的几种方法
oracle优化之生产系统不改代码解决SQL性能问题的几种方法
26-03-03 - Oracle网络服务基础(一)之监听器概念
Oracle网络服务基础(一)之监听器概念
26-03-03